vCISO
virtual Chief Information Security Officer
Overview

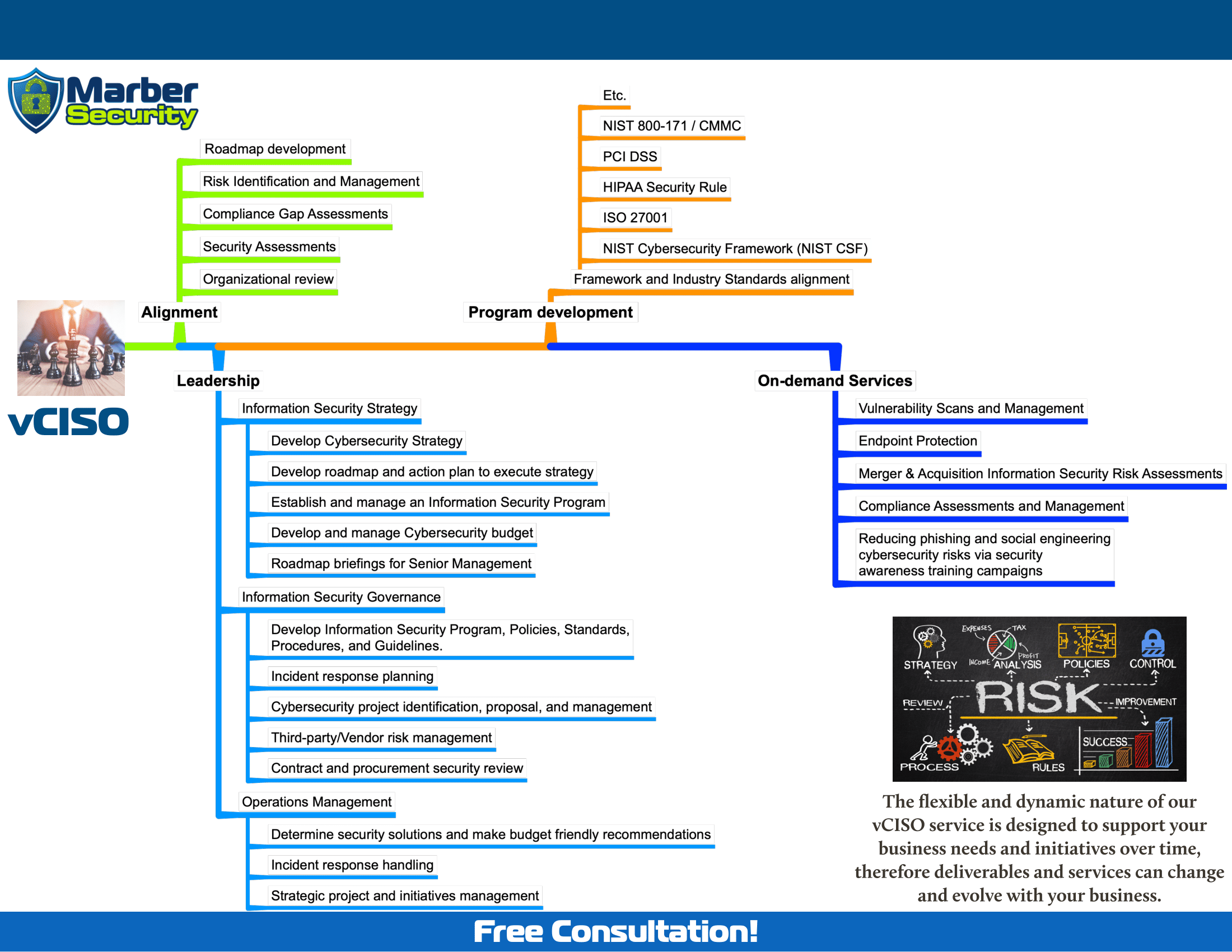
Information security incidents and data breaches over the past few years have led to organizations facing aggregate information security legal, regulatory, and contractual requirements to protect themselves and the data they accept, process, transmit and/or store. Our virtual Chief Information Security Officer (vCISO) is designed to help organizations establish and improve their information security posture to support their business needs and requirements. The vCISO service is intended to provide expertise associated with information security practitioners, including but not limited to providing:
Alignment with business needs and recommendations to help the organization:
Leadership by providing actionable cybersecurity strategy, governance, and operations management.
Program development by empowering organizations with knowledge and tools to help them establish and improve an Information Security Program that aligns with their business needs.
Expertise
Marber Security will help provide security alignment, leadership, and program development. The vCISO service provides access to certified and experienced security practitioners that can provide alignment, leadership, and program development.
Onboarding
To provide information security strategic and governance leadership, new vCISO engagements start with an Organizational review and a SCF 50 - Basic Security Assessment that lets us learn about your organizational needs and requirements. In this stage, clients share their current business, IT, and cybersecurity initiatives; areas of concern that require attention, and any known compliance, regulatory, or contractual information security requirements. Partnered with Marber Security, the client will collaboratively define a target security posture.
Success
An effective engagement and partnership require regular interaction with your organization’s senior IT staff and with senior management. In the process of delivering our services, we encourage you to contact us with any questions or concerns at vCISO@marbersecurity.com or at (833) 231-7087 x1.
Common Use Cases

The flexible and dynamic nature of our vCISO service is designed to support your business needs and initiatives over time, therefore deliverables and services can change and evolve with your business. Marber Security is most commonly asked to assist with:
Alignment
- Organizational review
- Security Assessments
- Compliance Gap Assessments
- Risk Identification and Management
- Roadmap development
Leadership
- Information Security Strategy
- Develop Cybersecurity Strategy
- Develop roadmap and action plan to execute strategy
- Establish and manage an Information Security Program
- Develop and manage Cybersecurity budget
- Roadmap briefings for senior management
- Information Security Governance
- Develop Information Security Program, Policies, Standards, Procedures, and Guidelines.
- Incident response planning
- Cybersecurity project identification, proposal, and management
- Third-party/Vendor risk management
- Contract and procurement security review
- Operations Management
- Determine security solutions and make budget-friendly recommendations
- Incident response handling
- Strategic project and initiatives management
Program development
- Framework and Industry Standards alignment
- NIST Cybersecurity Framework (NIST CSF)
- ISO 27001
- HIPAA Security Rule
- PCI DSS
- GLBA
- NIST 800-171 / CMMC
- and more
Other On-demand Services
- Vulnerability Scans and Management
- Endpoint Protection
- Ransomware Protection
- Internet & DNS Protection
- Password Security & 2FA
- Data Backup
- Email Security
- Merger & Acquisition Information Security Risk Assessments
- Compliance Assessments and Management
- Reducing phishing and social engineering cybersecurity risks via security awareness training campaigns
The vCISO may recommend security improvements to be performed by Marber Security or other qualified contractors/consultants.

A successful vCISO partnership is built upon alignment with your business needs, to help us develop the leadership strategy, and help implement an appropriate Information Security Program. We first get to know your business via an Organizational review, then get a broader view via a Basic Security Assessment. Both of these enable us to develop the security roadmap and make recommendations. New vCISO clients are onboarded through the following process:
- Organizational review – meetings with key internal stakeholders to review the organization’s business mission; organizational structure; business, IT, and cybersecurity needs; relative maturity of the security program and practices; and historical events that may impact security requirements.
- SCF 50 - Basic Security Assessment – a detailed and guided assessment of 50 questions using the Secure Controls Framework to review key organizational functions necessary to identify and improve the organization’s security posture.
- Security Roadmap development – identification and development of a security initiative roadmap informed by the information collected during the organizational review and the SCF 50 Basic Security Assessment.